Border security is no longer about manual checks and visual inspections. With rising threats such as vehicle-borne explosives, illegal smuggling, and concealed contraband, authorities require faster, smarter, and more reliable inspection technologies. A 3d under vehicle scanner for border security has become an essential tool for modern checkpoints, enabling security teams to inspect vehicles thoroughly without disrupting traffic flow.
UVSS delivers advanced under vehicle inspection solutions designed specifically for high-risk, high-traffic border environments where precision and speed are critical.
Why Vehicle Undercarriage Inspection Matters
The underside of a vehicle is one of the most common locations used to hide explosives, weapons, narcotics, and tracking devices. Traditional inspection methods, such as mirrors or manual searches, are slow and highly dependent on human attention.
A 3d under vehicle scanner for border security eliminates these limitations by capturing complete undercarriage images automatically. Every vehicle is scanned consistently, ensuring that no hidden threat goes unnoticed, regardless of traffic volume or operator fatigue.
What Makes 3D Scanning Different
Unlike conventional 2D systems, 3D scanning technology adds depth and multiple viewing angles. This allows security personnel to detect abnormalities that may not be visible in flat images.
Key advantages of 3D scanning include:
- Clear visualization of hidden compartments
- Better identification of foreign objects
- Improved differentiation between normal vehicle parts and threats
- Accurate comparison with baseline vehicle profiles
For border security operations, this level of detail significantly improves decision-making and threat response time.
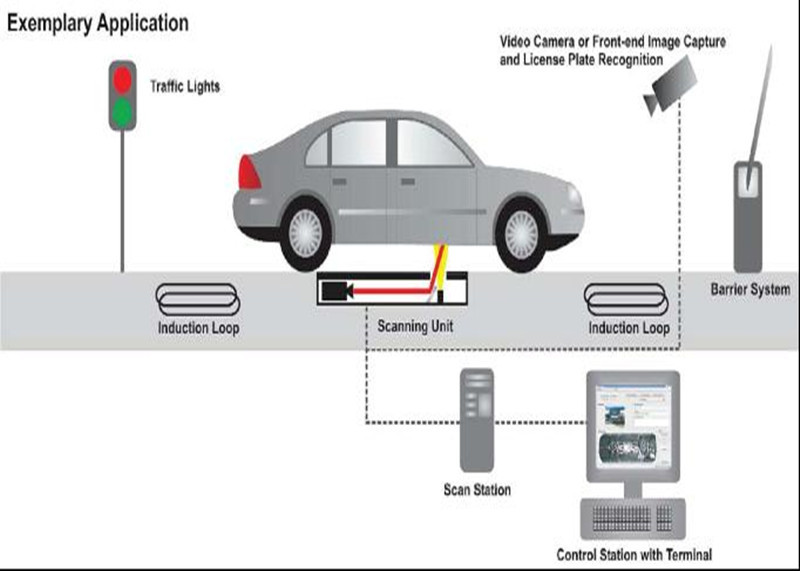
How a 3D Under Vehicle Inspection System Works
A modern under vehicle inspection system operates seamlessly as vehicles pass through a checkpoint.
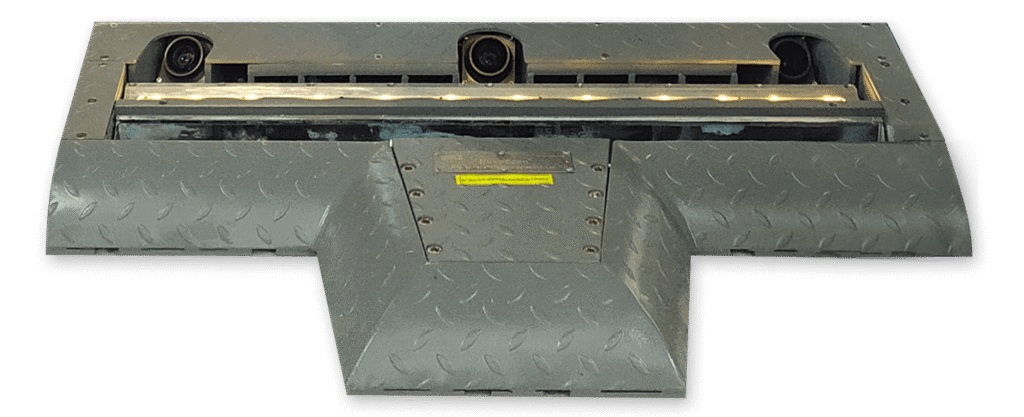
- Vehicles drive over a scanning platform embedded with high-resolution cameras
- Images of the undercarriage are captured instantly
- Advanced software constructs a detailed 3D image
- AI-powered analysis highlights suspicious objects
- Operators receive results in real time
This automated process ensures that inspections remain fast, accurate, and consistent, even during peak traffic hours.
Key Benefits for Border Security Operations
Faster Throughput
Border crossings often deal with thousands of vehicles daily. A 3d under vehicle scanner for border security allows inspections to be completed in seconds without stopping vehicles, reducing congestion and delays.
Higher Detection Accuracy
3D imaging combined with intelligent software dramatically improves detection rates for explosives, weapons, and contraband.
Reduced Human Risk
Security personnel no longer need to physically inspect vehicle undersides, minimizing exposure to potential threats.
Centralized Monitoring
All scans are stored digitally, enabling centralized monitoring, investigation support, and long-term security analysis.
Who Should Use Under Vehicle Inspection Systems
While border checkpoints are the primary application, under vehicle inspection systems are also essential for:
- Customs and immigration points
- Military and defense facilities
- Airports and seaports
- Government buildings
- High-security industrial zones
Any location that requires controlled vehicle access can benefit from UVSS technology.
Buy Under Vehicle Inspection System with Confidence
When organizations plan to buy under vehicle inspection system solutions, selecting the right technology partner is critical. Not all systems offer the same level of accuracy, durability, or intelligence.
Here are the most important factors to consider:
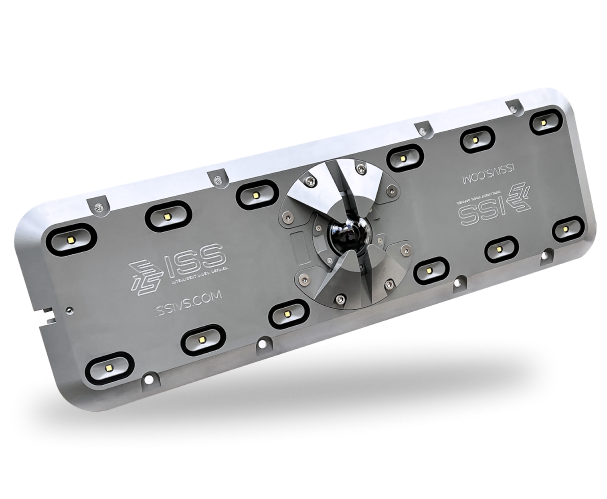
Advanced Imaging Technology
Ensure the system supports high-resolution 3D imaging for complete undercarriage visibility.
AI-Based Detection
Automated anomaly detection reduces reliance on manual review and improves response speed.
System Integration
The inspection system should integrate easily with access control, ANPR, and security management platforms.
Rugged Design
Border environments demand equipment that can operate reliably in dust, rain, heat, and heavy traffic conditions.
Scalability
A future-ready system should support expansion across multiple checkpoints or locations.
UVSS solutions are engineered to meet all these requirements, making them a trusted choice for mission-critical deployments.
Why UVSS Is the Right Choice
UVSS specializes in intelligent vehicle inspection technologies built for real-world security challenges. Our systems are designed to support continuous operation while delivering precise, actionable insights.
With UVSS, organizations gain:
- High-performance 3D scanning technology
- Reliable and fast inspection workflows
- Enhanced threat detection accuracy
- Long-term operational efficiency
- Scalable solutions for growing security needs
Choosing UVSS means investing in proven technology that strengthens perimeter security without compromising efficiency.
Future of Border Security Inspection
As threats become more sophisticated, security infrastructure must evolve. Manual inspections and outdated tools can no longer keep pace with modern risks.
A 3d under vehicle scanner for border security represents the future of vehicle inspection—combining automation, intelligence, and speed. Organizations that act now position themselves ahead of emerging threats while maintaining smooth border operations.
Final Thoughts
If you are planning to buy under vehicle inspection system technology for border security, accuracy and reliability should be your top priorities. Advanced 3D scanning systems from UVSS deliver unmatched visibility, faster inspections, and stronger protection at every checkpoint.
By adopting modern under vehicle inspection solutions, border authorities can enhance safety, reduce operational risks, and ensure that every vehicle entering secured areas is thoroughly inspected.