If you are searching for the best under vehicle scanning systems for airports, you are likely responsible for airport security, perimeter protection, or infrastructure safety. You need a reliable system that can detect threats under vehicles quickly and accurately without slowing down traffic.
Airports are high-risk and high-traffic environments. Every vehicle entering the premises — from cargo trucks to staff cars and service vehicles — must be inspected. Manual inspection is slow, risky, and not effective against modern threats. This is where advanced UVSS technology becomes essential.
At UVSS, we provide intelligent, high-speed, and fully automated under vehicle inspection systems designed specifically for airports.
Why Airports Need Advanced Under Vehicle Scanning

Airports are critical infrastructure. Security breaches can lead to serious consequences including:
- Unauthorized vehicle access
- Explosive threats
- Smuggling attempts
- Weapon concealment
- Terror-related risks
When searching for the best under vehicle scanning systems for airports, security managers typically want:
- Real-time vehicle undercarriage imaging
- Automatic number plate recognition (ANPR)
- High-resolution scanning
- AI-based threat detection
- Integration with existing airport security systems
- Fast vehicle throughput
Modern airport security requires layered protection. Perimeter fencing and CCTV are not enough. Vehicle inspection is a crucial security checkpoint.
What Is an Under Vehicle Scanning System (UVSS)?
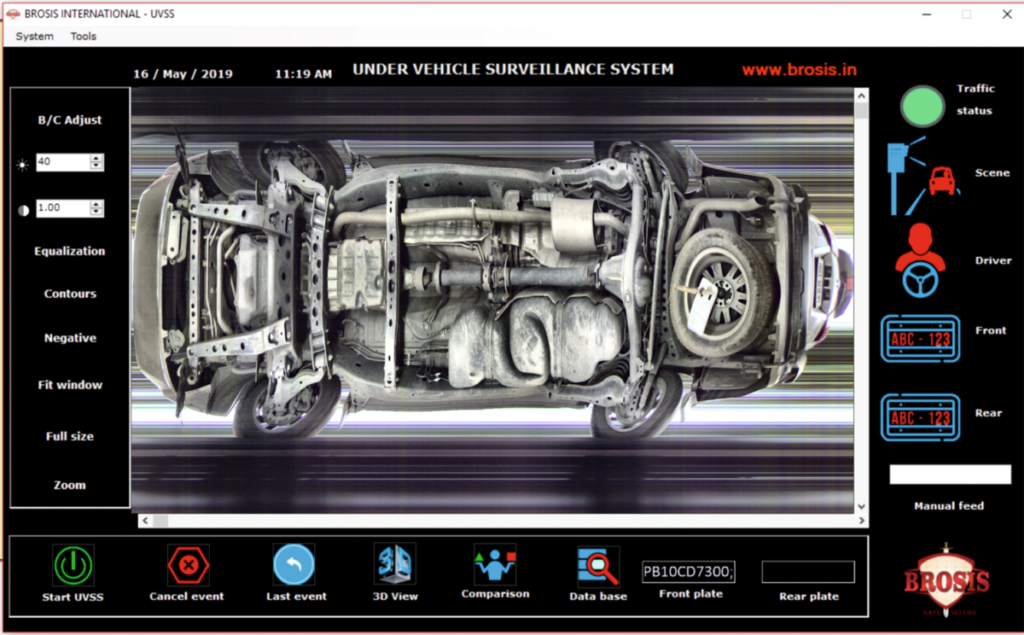
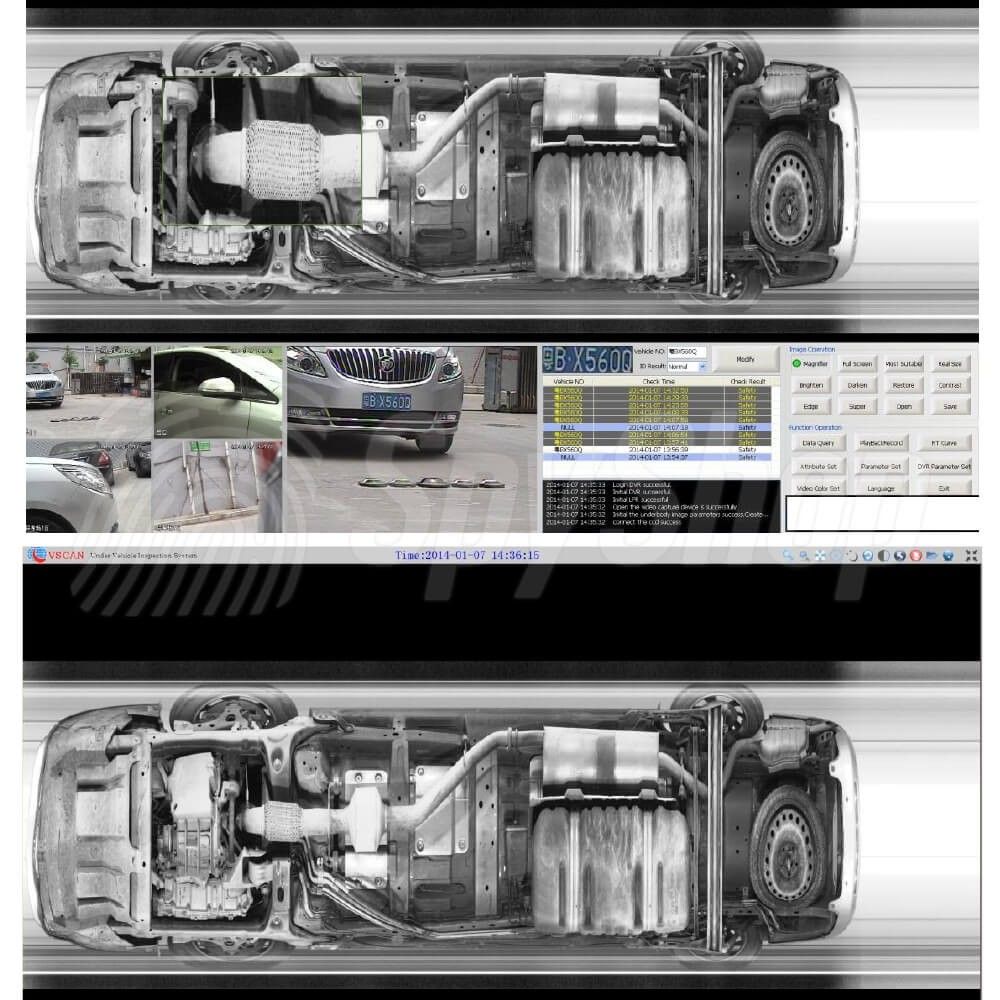
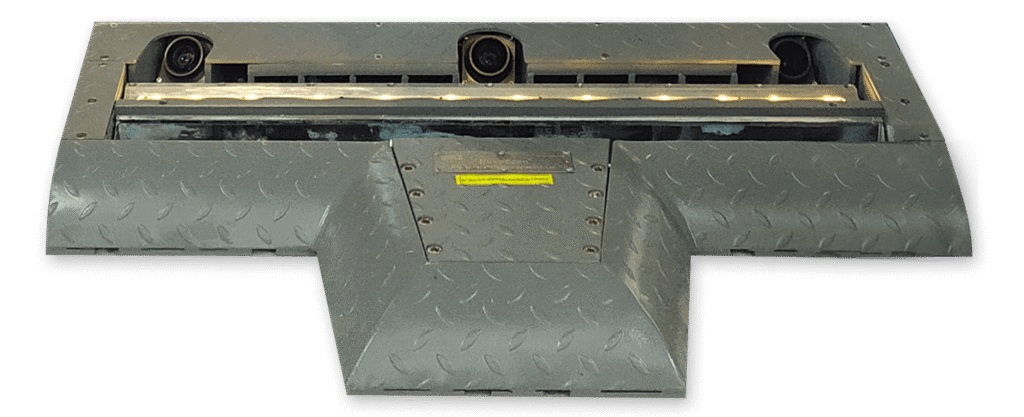
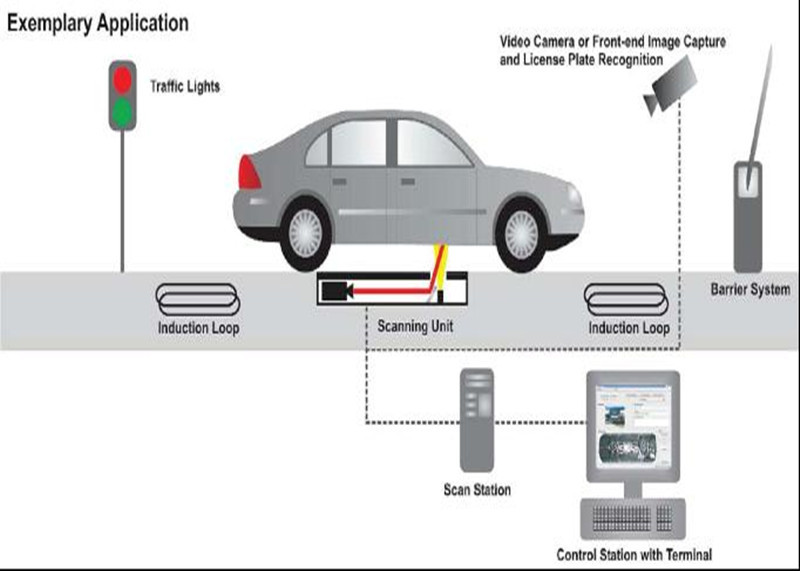
An under vehicle scanning system is an advanced security solution that captures high-resolution images of a vehicle’s undercarriage as it drives over a scanning unit.
The system typically includes:
- Ground-mounted scanning unit
- High-resolution line scan cameras
- LED lighting for clear imaging
- Control room monitoring software
- Automatic threat detection algorithms
- Data storage and reporting tools
The best under vehicle scanning systems for airports provide continuous scanning without requiring vehicles to stop completely, reducing congestion while maintaining security.
Key Features of the Best Systems for Airports
When airports evaluate the best under vehicle scanning systems for airports, they focus on performance, reliability, and compliance.
1. High-Speed Scanning
Airports handle thousands of vehicles daily. A good UVSS system must scan vehicles at varying speeds without losing image clarity.
2. High-Resolution Imaging
Clear imaging is critical to detect:
- Explosive devices
- Hidden packages
- Suspicious modifications
- Foreign objects
Advanced UVSS systems provide panoramic undercarriage images for detailed inspection.
3. AI-Based Threat Detection
Modern systems use artificial intelligence to compare vehicle images with stored references. Any unusual object or change triggers an alert.
4. Automatic Number Plate Recognition (ANPR)
ANPR integration helps security teams:
- Track vehicle entry history
- Blacklist suspicious vehicles
- Maintain digital logs
- Improve investigation efficiency
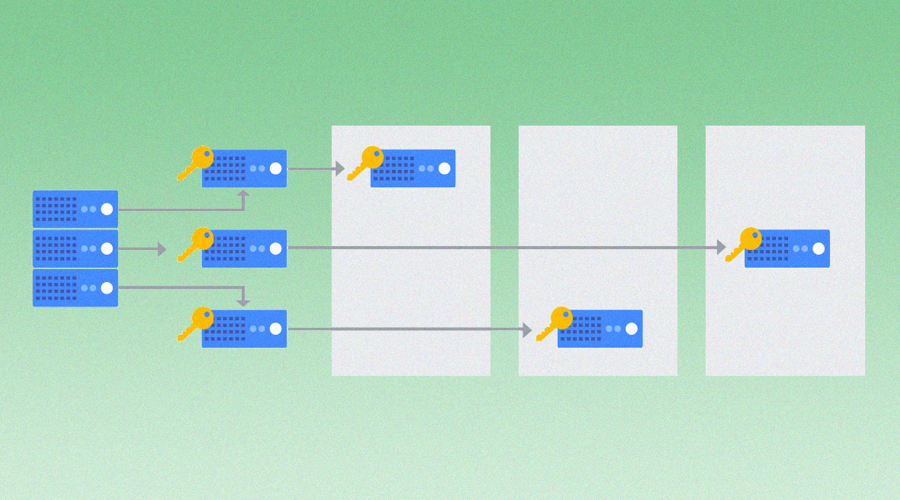
5. Integration with Airport Security Systems
The best under vehicle scanning systems for airports integrate with:
- Access control systems
- CCTV surveillance
- Boom barriers
- Command and control centers
- Perimeter intrusion detection systems
UVSS solutions are designed to integrate smoothly into existing airport infrastructure.
Types of UVSS Solutions for Airports
Different airports require different configurations. Here are common types:
Fixed UVSS Systems
Installed permanently at airport entry and exit gates. Ideal for high-security checkpoints.
Portable UVSS Systems
Mobile systems used during temporary security operations or high-alert situations.
Integrated UVSS with Access Control
Combines vehicle scanning with gate barriers and RFID vehicle tagging for complete control.
UVSS provides scalable systems depending on airport size and traffic volume.
Benefits of Installing the Best Under Vehicle Scanning Systems
Choosing the best under vehicle scanning systems for airports provides long-term operational and security advantages.
Enhanced Threat Detection
Automated detection minimizes human error and improves response time.
Faster Vehicle Processing
Non-intrusive scanning reduces delays while maintaining strict security.
24/7 Monitoring
Systems operate continuously without fatigue or inconsistency.
Digital Record Keeping
Every scanned vehicle is logged with time, date, and image data.
Improved Compliance
Airports must comply with national and international aviation security regulations. UVSS helps meet these standards.
Why Choose UVSS for Airport Security?
At UVSS, we understand that airports require advanced and reliable protection. Our systems are built for:
- Heavy traffic conditions
- Harsh weather environments
- Continuous 24/7 operation
- High-threat scenarios
We focus on:
- High-definition imaging
- AI-powered detection
- Fast installation
- Minimal maintenance
- Scalable architecture
When airport authorities look for the best under vehicle scanning systems for airports, they choose solutions that reduce risk while maintaining operational efficiency. UVSS delivers both.
Important Factors to Consider Before Buying
Before selecting the best under vehicle scanning systems for airports, decision-makers should evaluate:
- Daily vehicle volume
- Required scanning speed
- Environmental conditions
- Integration needs
- Budget allocation
- Compliance requirements
- Future expansion plans
A professional risk assessment ensures the right solution is deployed.
How UVSS Improves Airport Perimeter Security
Vehicle checkpoints are part of a layered security approach. UVSS works alongside:
- Perimeter fencing
- Surveillance cameras
- Access control gates
- Security personnel
- Explosive detection systems
The goal is to prevent threats before they reach critical airport zones.
With smart alerts and instant image comparison, UVSS solutions enhance decision-making in real time.
Future Trends in Airport Vehicle Scanning
The demand for the best under vehicle scanning systems for airports is growing due to increasing global security challenges.
Emerging trends include:
- AI-powered anomaly detection
- Cloud-based monitoring
- Centralized multi-location control
- Advanced data analytics
- Integration with smart airport systems
UVSS continues to innovate to meet evolving airport security needs.
Final Thoughts
If you are searching for the best under vehicle scanning systems for airports, your goal is clear: maximum security without disrupting operations.
Airports face constant threats, and vehicle inspection is a critical control point. Manual inspection is no longer sufficient. Modern UVSS technology provides:
- Automated detection
- Real-time imaging
- Seamless integration
- High-speed scanning
- Reliable 24/7 operation
At UVSS, we provide advanced solutions designed specifically for airport environments. Our systems are secure, scalable, and built for critical infrastructure protection.
Investing in the right UVSS solution is not just about technology — it is about safeguarding passengers, staff, and national security.
Contact Us for a free quote